Cryptography and the Intelligence Community: The Future of Encryption (2022)
Chapter: 5 Scenarios
5
Scenarios
As discussed in Chapter 3, the objective of the committee was to select three scenarios that would be stressful for planning and pose a wide range of situations, as well as meet criteria derived from the focal question. Although each of the drivers is important in developing the scenarios, the committee determined that exploring the edge cases presented by the Systems (Mature/Chaotic) and Scientific Advances (Disruptive/Predictable) drivers in combination with a “Fragmented” Society and Governance driver would provide the most value to the Intelligence Community. Choosing these scenarios allowed members to explore two technology breakthroughs that would impact existing public key cryptographic algorithms: a breakthrough in quantum computing and the discovery of a new cryptanalytic method usable on classical computers. These scenarios also provided opportunities to highlight the important role that systems and cybersecurity will play in the future. Last, the committee selected three scenarios with a “Fragmented” Society and Governance driver, because such scenarios presented the greatest challenge to the Intelligence Community and, the committee agreed, seemed the more likely direction in which global events were trending. “Fragmented” scenarios also are more complex as they do not assume homogeneity with respect to legal, cultural, privacy, and consumer issues, and selecting “Fragmented” scenarios pushed members to consider unique regional perspectives and uses.
Table 5.1 shows the endpoints associated with the eight possible scenarios, and Appendix C provides a brief summary description of each. The following sections describe each of the three scenarios—Scenarios 2, 5, and 6—that the committee selected for in-depth exploration. In each case, the scenario description is presented as a historical “look back” from a future perspective. Each contains a table that summarizes the scenario and a description of the scenario in detail.
SCENARIO 2: A BRAVE AND EXPENSIVE NEW WORLD
In 2038, China announced the availability of a large-scale, commercial quantum computer service. The Chinese intelligence services have supported this development and “tested” it for several years on encrypted information of domestic and foreign targets. Several other advanced nations, including the United States, are understood to have similar capabilities but have not advertised the fact. (See Box 5.1.)
Although China was first to announce the breakthrough, the pace of scientific and technological advances throughout the previous decades made the possibility seem increasingly likely, and a breakthrough appeared imminent. A series of advances had resulted in commercially available noisy intermediate-scale quantum (NISQ)
computers. These machines were optimized for chemistry simulations, and mostly marketed to pharmaceutical and biotech companies for drug discovery and agricultural applications. After an algorithmic advance that allowed a practical speedup for deep learning algorithms on NISQ computers, the major cloud computing platforms began offering time on quantum computing coprocessors. The early commercially available computers had error rates that were too high to run Shor’s algorithm to break public-key encryption, but this was no matter: the market was much more interested in large-scale commercial applications. However, once several tech companies (IBM, Microsoft, Intel, and a handful of start-ups) began competing to sell quantum computing services on the commercial market, there was a rapid improvement in error rates and scaling behavior. It seemed clear that arbitrary scaling could be reached within a few years.
Because quantum computing that would threaten public-key encryption seemed like such a real possibility, however, companies and countries invested time and resources to understand how to leverage the opportunities and prepare to mitigate the risks. All of the talk about quantum computing drove a sense of urgency in the cryptographic and information technology communities, forcing many to realize that the threat to public-key cryptography was no longer theoretical and it was time to complete the transition to post-quantum cryptography (PQC). Scenario 2, “A Brave and Expensive New World,” is described in Table 5.2.
Developers and architects of systems regrouped from a turbulent time. During the early 2020s, cyber-attacks on physical infrastructure and information continued to increase. It did not matter whether these were nation states, criminal enterprises, or individuals—they were disruptive, costly, and dangerous. Over the decade, countries and companies invested heavily in improving cybersecurity, focusing on high quality standards and implementations. Pressures by concerned commercial customers and individuals added to those imposed by major powers’ governments (such as U.S. Executive Order 14028) and drove technology vendors and large users to follow through on achieving improved security. Fewer bugs in systems made vulnerabilities progressively rarer and nations found it increasingly difficult to undermine the confidentiality, integrity, or availability of adversaries’ information systems. Mature systems and strong cybersecurity made the transition to PQC on par with past (and technically simpler) transitions. There were challenges, but, for the most part, the move happened with little global disruption.
The move to PQC was, for the most part, an orderly transition, but the changing geopolitical landscape over the decade led to a fracturing of standards and the rise of national algorithms (i.e., country-specific cryptographic technologies) with far-reaching consequences. The same sense of urgency that drove the transition to PQC provided an impetus for countries to start developing and implementing their own standards. For example, the National Institute of Standards and Technology (NIST) in the United States and its counterparts in China and Europe each developed standards that were accepted by the International Organization for Standardization. In the early 2030s,
TABLE 5.1 Endpoints That Define the Eight Possible Scenarios
| Scenario | Scientific Advance | Society and Governance | Systems |
|---|---|---|---|
| 1 | Predictable | Fragmented | Mature |
| 2 | Disruptive | Fragmented | Mature |
| 3 | Predictable | Global | Mature |
| 4 | Disruptive | Global | Mature |
| 5 | Predictable | Fragmented | Chaotic |
| 6 | Disruptive | Fragmented | Chaotic |
| 7 | Predictable | Global | Chaotic |
| 8 | Disruptive | Global | Chaotic |
TABLE 5.2 Scenario 2: A Brave and Expensive New World
| Scenario Title | Driver Endpoints | Highlight |
|---|---|---|
| A Brave and Expensive New World |  |
A breakthrough in quantum computing is balanced with more secure systems and software and an orderly transition to post-quantum encryption. |
| Scenario Description | ||
|
This scenario posits that a breakthrough in quantum computing is offset by an orderly transition to post-quantum encryption and other emerging cryptographic techniques, because of earlier investments in systems and cybersecurity. Overall, the balance now favors defense. However, the global political picture remains fragmented. The bottom line for the Intelligence Community is that offensive cryptography efforts have become more difficult, and the alliance structure that is a major plus for U.S. intelligence is less reliable and more fluid. In this scenario, a major issue for U.S. intelligence will be its ability to discern, far enough in advance, the development of a reliable, large-scale quantum computer. This is of crucial importance to this scenario, which posits the development of more secure systems because governments and the private sector take seriously the need for improved cybersecurity and invest in the development and deployment of much more robust systems. Even if such a quantum computing breakthrough did not occur, there are obvious benefits in enhanced systems and cybersecurity. If these steps are taken early enough and on a wide basis, then the transition to a post-quantum world would be orderly. It will be important for U.S. intelligence to be able to discern in advance the development of a reliable large-scale quantum computer both to ensure that progress toward post-quantum encryption is sufficient for defensive purposes and to assess potential offensive opportunities. International relations in this scenario fragment into a small number of blocs composed of a few major powers (the United States, the European Union, China) and a large number of dependent powers that, for the most part, rely on a major power for economic, technological, and defense support. Technology and encryption are similarly fragmented with blocs sharing common approaches to encryption and inter-bloc communications relying on weak “least common denominator” encryption. Within blocs, government surveillance is the norm although some governments and some private companies use new capabilities for processing encrypted data to protect sensitive processing. |
||
Europe, led by Germany’s BSI,1 decided that, although NIST ran a good process, they had selected the wrong winners; therefore, the European Union (EU) determined that it would select a different set of winners. These “Big Three” powers saw opportunities for influence and, rather than align on a single standard, each major power forced vendors to implement by default and individual and corporate users to adopt their own preferred national suite of encryption algorithms.
This fragmentation continued over the intervening years, and the “Big Three”—China, Europe, and the United States—have emerged as major powers exerting regional and digital influence over their own blocs of loosely allied nations. Some countries have plotted their own course, for the most part, and move between the major spheres of influence, depending on where their interests lie—the fragmented nature of global politics means that alliances are constantly shifting. In the world of 2040, the United States finds that, rather than a stable of trusted allies, it has developed a series of relationships based on the situation and the interests at hand.
Shifting alliances and diminishing trust compared to the 2020s and before mean that, at this point, there is very little globalism; instead, the “Big Three” blocs concentrate trade and technology within their own systems. Each major power has developed and deployed its own information technology systems, quite distinct from the others, with its own hardware designs and implementations, software, and development processes. Each also has its own mobile wireless system, its own fiber optic networks and technology, its own extensive low-Earth orbit communication satellite systems, its own Global Positioning System equivalent, and its own integrated infrastructure for autonomous transportation (air and ground). After a number of physical and cyber infrastructure attacks in the early 2020s, the “Big Three” invested significant resources in building solid defenses into their information systems; in fact, the systems of 2030 are much more secure than the systems of a decade ago—they simply do what they are designed to do.
Global technology firms do not exist as they did a decade ago. In the United States, firms such as Meta, Amazon, and Google could not overcome the backlash from questions of privacy and disinformation, and Congress had stepped in to regulate them heavily. For different reasons, government and regulatory authorities in Europe and China took similar steps, encouraging the rise of national champions that would control the flow of information
___________________
1 Bundesamt für Sicherheit in der Informationstechnik: German Federal Office for Information Security.
within their spheres of influence. Russia and India have attempted to build their own competing systems, but their influence and reach do not compare to those of the “Big Three” major powers.
Dependent nations rely on the national algorithms from a major power for their international banking systems, their information technology, and so forth. In most cases, they adopt the cryptographic systems of their major power partner but are generally suspicious that there may be backdoors or weaknesses in such systems and are certain that they are not getting “the really good stuff.” They are also heavily reliant on the “Big Three’’ for vaccines and other bio-engineering products; new diseases are sweeping through all the time, endangering both people and agriculture. There is much speculation that these diseases are man-made, but no proof. In any case, most nations rely on a major power for protection and to help arbitrate the international issues driven by climate change such as shortages of water and mass migrations.
Trade among blocs exists, although the underlying communications infrastructure is something of a mess. Because each bloc requires support for its own cryptographic algorithms, vendors simply implement support for a long list of algorithm variants that are all considered to be roughly reasonable choices. International corporations maintain redundant parallel internal information technology (IT) infrastructure in order to satisfy the complex regulatory environments of different regions and major powers. EU privacy regulation has begun requiring that customer records be stored and operated upon in entirely encrypted form when possible. This has resulted in commercially available multi-party computation (MPC) and encrypted database search platforms with sufficient performance and usability to be viable alternatives to their unencrypted counterparts for some applications. The technical details and privacy guarantees of these schemes are widely misunderstood by governments and end users.
Although the complexity of true fully homomorphic encryption (FHE) has not improved enough to allow its use for nontrivial systems, the acronym FHE has ended up being used by nontechnical users as a generic term applying to just about any privacy-preserving system. Several traditionally democratic countries have mandated law enforcement access to encrypted communications, with some also mandating cryptographic schemes for accountability and tracing for all electronic speech. The particular implementations have been left up to service providers. Citizens assume that intelligence agencies regularly gain access to the law enforcement access portals to surveil communications at will. The major encrypted communication protocols all include complex cipher negotiation steps; a few downgrade attacks are published in the academic literature, but mature systems development has limited the real-world impact of such attacks.
If there is one thing that people around the world share in this scenario, it is their discontent. They are deeply suspicious and prone to expect the worst from their own governments and their fellow citizens, but the manifestations are quite different in the blocs. The United States has long attempted to rally support from its own citizens by emphasizing transparency; other nations have implemented extremely intrusive “thought control” regimes by intense monitoring of all citizens, backed up by extensive use of artificial intelligence to collect and analyze data. Even in the European Union, despite a historical commitment to human rights, a rise in terrorism and threats posed by massive illegal immigration from Asia and Africa led to increased efforts to monitor and control the population. Whatever the approach, the end results are similar: a large majority of citizens feel that their government is controlled by corrupt elites who are trying to suppress them and view their fellow citizens with deep distrust.
One additional dynamic is at play. Many of the Major Powers have aging populations where a rapidly shrinking workforce must support an ever-larger contingent of retirees. Of course, artificial intelligence and robotics help in this regard, but this trend brings two big societal strains that threaten the national and international order.2 Within a Major Power, younger generations are becoming ever more frustrated with their incomes being transferred to ever-larger numbers of relatively affluent retirees. And within the larger bloc, the dependent nations are on the whole much younger—and more dynamic—than the corresponding Major Power. Both strains tend to undermine the Major Power government, leading to a pervasive sense of unfairness and instability for all Major Powers.
Warning Signals for Scenario 2
Table 5.3 summarizes some key developments associated with Scenario 2, along with warning signals that might indicate to the Intelligence Community that this scenario is emerging.
Risks and Opportunities in Scenario 2
“A Brave and Expensive New World” appears to be great powers jockeying for territory and influence across a series of constantly changing alliances. But in this scenario, technology has advanced to the point where territory has been replaced by information as a symbol of power. Indeed, companies that are influenced by great powers or companies that wield great power and influence in their own right because of their technological advantages also have to be considered as significant players in this scenario. The combination of Disruptive, Fragmented, and Mature will present its own unique challenges for the Intelligence Community. For example, in a Fragmented scenario, nations are less likely to trust each other or share secrets and resources. Looking more locally, the Intelligence Community might face the challenge of recruiting, hiring, and retaining high-quality staff. With mature systems being pervasive (as described by the endpoint on the Systems driver), accessing information will have to rely less on technology and exploiting bugs and more on overt surveillance and human intelligence and exploiting people—presenting an insider threat challenge for intelligence services across the globe.
Pervasive mature systems would have deep, far-reaching effects across society. In this scenario, cybersecurity is very high quality and breaks are rare. Consequently, nations find it very difficult to gather intelligence from, or disrupt, information systems. This would be a game changer for the Intelligence Community.
___________________
2 See, for example, B. Nichiporuk, 2000, Demographics and the Changing National Security Environment, RAND Corporation, Santa Monica, CA.
TABLE 5.3 Key Developments and Warning Signals for Scenario 2: A Brave and Expensive New World
| Development | Warning Signal |
|---|---|
| “A series of advances had resulted in commercially available noisy intermediate scale quantum (NISQ) computer.” | The Intelligence Community should be paying attention to the commercial world and who is developing a NISQ and how quickly. |
| “The major cloud computing platforms began offering time on quantum computing coprocessors.” | Is quantum computing being offered as a service? Even if it is not scalable, the Intelligence Community should be monitoring who is selling and who is buying these services. |
| “During the early 2020s, cyberattacks on physical infrastructure and information continued to increase. It did not matter whether these were nation states, criminal enterprises, or individuals—they were disruptive, costly, and dangerous. Over the decade, countries and companies invested heavily in improving cybersecurity, focusing on high quality standards and implementations.” | Are there more attacks over the next few years; are more high-quality standards and (especially) implementations becoming available? If so, this world might be emerging; if not, we might be on a Chaotic Systems axis. |
| “But the changing geopolitical landscape over the decade led to a fracturing of standards and the rise of national algorithms (that is, country-specific cryptographic technologies) with far-reaching consequences.” | Are national standards and encryption algorithms emerging around the world or are countries continuing to engage in and adopt international standards? |
| “In the United States, firms such as Facebook, Apple, and Google could not overcome the backlash from questions of privacy and disinformation, and Congress had stepped in to regulate them heavily. For different reasons, government and regulatory authorities in Europe and China took similar steps, encouraging the rise of national champions that would control the flow of information within their spheres of influence.” | Is Congress regulating the major technology companies more heavily? Are Europe and China taking similar steps? |
Risks for the Intelligence Community in Scenario 2 include the following:
- Cryptographic breakthroughs pose significant risk: Although there was not a quantum breakthrough until the late 2030s, the emergence of quantum computers means that information that was encrypted using public-key encryption algorithms vulnerable to quantum computer attacks and collected and stored by an adversary is vulnerable to disclosure. Once such information is collected, there is nothing the originator can do to protect it, but there is a need for an inventory, assessment of potential damage, and development of mitigation plans. In addition, any data previously collected by the Intelligence Community that was secured by vulnerable encryption could be accessible.
- Insider threat: As distrust in the U.S. government increases, the risk from insider threat grows. In addition, given the strength of cybersecurity across the globe, the premium placed on human assets in organizations will only increase the demand for insider access.
- Recruiting, hiring, and retaining the “best and the brightest”: Employee quality is a key risk. Will the United States and the Intelligence Community have the talent to be successful, particularly if the United States ceases to attract students and faculty from around the world?
- Weakening and shifting alliances: In a fragmented scenario, the United States should not assume that traditional long-term allies remain. As trust and collaboration recede, collection efforts grow more expensive and will surely need deep triage. With ever-shifting bilateral alliances, it may be hard (slow) to pivot to new targets or allies; and it is unwise to share important secrets with any nation that seems likely to switch alliances.
- Mature implementations of advanced cryptography: Multi-party computation may permit limited or controlled data sharing with allies, but if used by adversaries it could be an impediment to collection efforts that would historically have targeted plaintext. Similarly, mature implementations of anonymous cryptocurrencies would make following money flows much more difficult.
- Too many targets: If each country, or each region, is using its own unique system or form of encryption it is possible that the Intelligence Community would not have the resources to monitor and penetrate all systems
of interest. Fragmentation of the scenario’s information infrastructures increases the cost of intelligence collection from information systems, as every system requires its own tailored implementation.
Opportunities for the Intelligence Community in Scenario 2 include the following:
- The gloves come off: Perhaps there will be fewer problems of technical blowback as globalism recedes; regionalization of systems and technology means that a different region is considered “other,” as opposed to today where uniform standards and systems mean shared risk. Tools used to penetrate other nations may not also work against the United States. The Intelligence Community may also be able to exploit the seams in fragmented international systems, as the possible need to convert from one encryption protocol to another or to use weak “interoperable” systems may create exploitable weakness. In addition, the Intelligence Community may be able to use new analytic techniques against laggards in the transition to post-quantum.
- Exploiting human assets/insider threat: As the Intelligence Community recognizes that intelligence gains are less likely to come through attempted surveillance of adversaries’ well-defended networks, the community will devote more resources to recruiting and utilizing human assets in a far broader way. This task will be facilitated mostly by the greater willingness of disaffected individuals in this scenario to work against governments they distrust or even disdain, and partly by the fact that in a fractured geo-political situation, there would be multiple opportunities (potentially within an adversary country and across a wider number of adversaries) to find potential human intelligence assets who could add value. Such assets could help penetrate otherwise difficult networks and communications, and, through the ability of human sources to report on other types of information, would help offset the intelligence loss stemming from inaccessible networks. Properly placed assets could also facilitate technical attacks on their countries’ cryptographic systems by influencing national encryption standards while they were under development.
- New opportunities: If mature implementations become available for computation on encrypted data, this may open novel opportunities. Computation may become possible in untrusted or partially trusted environments such as other regions or allied government facilities using cryptographic techniques for “privacy-preserving transparency” (via MPC and zero knowledge).
Actions Relevant to Scenario 2
- Move to mature systems: This will require enormous effort across the United States, as the current status is at the “chaotic” end of the spectrum for nearly all systems. It is not clear that anyone really understands the implications of good cybersecurity because there is no real-world experience to draw on. It is also unclear how to move toward such systems in practice, although the 2021 cybersecurity executive order appears to be an attempt to move in that direction. This issue is much larger than the Intelligence Community and would require effort from major companies, researchers and start-ups, educational institutions, and the U.S. government. It is likely that very heavy investments would be required for research but especially for real-world implementations. As mature systems become available, the Intelligence Community must introduce new, more resilient IT very quickly (not over decades) and as needed abandon less-important IT infrastructure that cannot be quickly secured.
- Focus on ensuring that the United States can provide an adequate supply of high-quality, trustworthy staff: Although the large number of foreign-born students in science, technology, engineering, and mathematics (STEM) is a major advantage for our country, it should not be taken as a given and may not continue. The U.S. government should work toward considerable improvement in K–12 mathematics and science education, in particular. Advanced cryptographic research is poorly and unevenly funded in the United States; steady, long-term funding should be available for graduate students in cryptography and for efforts that may lead to mature systems (e.g., practical assured programming languages).
- Invest in technologies that can enhance the U.S. posture for both offense and defense: Potential areas of investment for defense include safer programming languages, improved toolchains, and formal verification. Other areas to consider for improving defense include realistic applications for the deployment of computing
- Limit/mitigate fragmentation, both in technologies and between the United States and allies: The Intelligence Community and the United States will need to consult with current allies and try to leverage purchasing power to push common standards and increase implementation maturity. The Intelligence Community will need to emphasize its efforts to preserve existing relationships with allies, but potentially plan to pivot toward new, perhaps short-term relationships. Such a pivot will require political resources, knowledge of other cultures, and tending such relationships. The Intelligence Community can also cooperate with other expert agencies, such as the Department of Homeland Security and NIST, to ensure appeal to the broadest audience worldwide. Last, because technology fragmentation is a key feature of this scenario, the Intelligence Community needs to learn new technologies and standards; there will be many more of them than at present, and with a higher rate of disruptive scientific advances.
- Examine resource and funding priorities: Collection will be much more difficult and will rely far more on human intelligence than on breaking into computer systems and intercepting communication. There is a multiplicity of hardware platforms, software, and communications systems without a central point; this combination will be very challenging, and ultimately have budgetary implications. In addition, a Fragmented scenario two decades from now means that the United States might not be able to rely on traditional alliances and will need to consider the implications for intelligence collection and resources.
on encrypted data and applications of trusted execution environments. On the offensive side, finding applications for noisy intermediate-scale quantum computers that could lead to a virtuous cycle in quantum computing technology could pay dividends.
SCENARIO 5: THE KNOWN WORLD, ONLY MORE SO
In 2030, the breakthrough for scalable quantum computing is far off; perhaps even more surprising is the fact that there have been few encryption-related mathematical breakthroughs globally. Both objectives have had their fair share of investment and attention, but neither quantum computing nor classical mathematics have had a breakthrough moment. Without the sense of urgency that a cryptanalytic breakthrough would drive, global society has been slow to make the transition to PQC algorithms for the past decade. Forward-leaning companies and countries have invested time and money into the effort, but the transition has been uneven across the globe, resulting in incompatibility, introducing bugs and, in some cases, creating new vulnerabilities or breaking existing communications infrastructure. Scenario 5, “The Known World, Only More So,” is described in Table 5.4.
The number of Internet of Things (IoT) devices has grown exponentially over the past two decades from almost 8.75 billion in 2020 to more than 250 billion in 2030 and today, in 2040, it is estimated that for each person on the planet there are approximately 1,000 connected devices. Further complicating the issue, the transition from 5G to 6G was messy and uneven across the globe. This combination of circumstances contributed to making life easier for “offense” over the course of the decade, as there were plenty of bugs in systems to exploit, driven by a reliance on poor quality code, inconsistent support for patching of security vulnerabilities, and a lack of common standards. Threat actors recognized that a messy transition to post-quantum algorithms would present an opportunity: there would be a target-rich environment and the payoff would be commensurate with the investment required.
The lack of common standards did not come as a surprise to those watching events unfold over the past decade. With no imminent threat of scalable quantum computers or classical breakthroughs that experts had said could arrive by 2030, there was no sense of urgency to align on a single, advanced global standard. The standardization process was beset by repeated delays and technical difficulties. After NIST released its final round choices for quantum resistant algorithms, the National Security Agency (NSA) raised and then escalated through the National Security Council which approved it, a request that NIST modify the parameters for the algebraically structured lattice algorithms. However, they refused to provide a detailed public explanation, leading to an uproar and rumors of either some kind of unreleased algorithmic attack against ring-LWE or an attempted backdoor.
TABLE 5.4 Scenario 5: The Known World, Only More So
| Scenario Title | Driver Endpoints | Highlight |
|---|---|---|
| The Known World, Only More So | 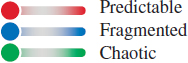 |
With no major breakthroughs and a continued lack of focus on systems and security, breaches remain common; meanwhile, the slow pace of technology change has allowed emerging competitors the chance to “catch up.” |
| Scenario Description | ||
|
This scenario posits that there are no major breakthroughs regarding a quantum computer, as well as a continued lack of focus on systems and security. Therefore, system breaches remain common. Also, the slow pace of technology change has allowed emerging competitors the chance to “catch up.” The overall balance continues to favor offense. The key issue under this scenario for U.S. intelligence is the broadening of the threat. We are already in a world where many states and a growing number of non-state actors pose threats to U.S. and allied interests. These threats will likely increase in number and severity in this scenario, potentially compounded by weakening of traditional alliances and partnerships. At the same time, a world of this sort remains a “target rich” environment for U.S. intelligence collection efforts. The constantly growing Internet of Things (IoT) also adds to this threat and to the opportunity. There is also the question of what tools, if any, the Intelligence Community should develop to respond to/retaliate against such attacks. Policies and decisions to do so belong to the policy community but the Intelligence Community should be prepared to offer a range of responsive options. Success in this scenario requires a very serious assessment of U.S.—meaning government at all levels and the private sector—vulnerabilities, in order to take steps to ameliorate or eliminate them. Given that this is the world we largely know at present, it may be difficult to motivate people and organizations to make changes that appear to be expensive and time consuming for perhaps modest gains in security. Private sector firms may also be wary, if not suspicious, about government efforts to foster changes. The measures in the Biden administration executive order are largely voluntary. Legislation may be necessary (like seat belt and speed limit laws) to foster real change. The Intelligence Community could be asked to give advice as to what measures are needed, although this sort of participation by U.S. intelligence is likely to foster greater suspicion about backdoors or other means of government intrusion. |
||
In response to these rumors, the European Union launched its own “independent” algorithm standardization process, which itself was beset with controversy after a set of leaked emails suggested that the Brainpool3 elliptic curve parameters had been manipulated by Germany’s BSI to permit a previously unknown trapdoor of unknown cryptanalytic impact. A segment of the cryptographic community retaliated by boycotting both contests and organizing a non-governmentally affiliated algorithm contest. This resulted in a mess of competing cryptographic standards and recommendations: NIST, an EU standard that eventually adopted the original lattice parameters that had been modified by NSA, and the grassroots cryptographic effort settled on a variant of Supersingular Isogeny Key Encapsulation (SIKE) and hash-based signatures that had widespread support among the tech industry.
The Internet Engineering Task Force was mired in discussions for years about how to incorporate algorithm negotiation into Transport Layer Security (TLS) and other higher-level protocols; the world was left with an officially supported set of TLS cipher suites that pointedly excluded the modified NIST algorithms, as well as Request for Comments–documented unofficial TLS extensions for the NIST algorithms and a number of other regionally standardized algorithms. This messy debate slowed the adoption of post-quantum algorithms and protocol upgrades by more than a decade.
In the meantime, the controversy over both classical and PQC algorithms as well as the general fragmentation of technology led to an increasingly complex regulatory and cultural situation with respect to cross-border network communications. Only vestiges of the open web, email, and other network protocols that dominated the history of the public Internet remain. Instead, communications and information have been mediated largely through individual apps. Users have become accustomed to installing custom “region” drivers and virtual private network (VPN) software that install the national algorithms, local government root certificates, and other cryptographic parameters required to access network resources in a given country.4
___________________
3 M. Lochter and J. Merkle, 2010, “Elliptic Curve Cryptography (ECC) Brainpool Standard Curves and Curve Generation,” Independent Submission to the Internet Engineering Task Force, Request for Comments: 5639, March, https://www.ietf.org/rfc/rfc5639.txt.
4 Krebs on Security, 2021, “Adventures in Contacting the Russian FSB,” June 7, https://krebsonsecurity.com/2021/06/adventures-in-contacting-the-russian-fsb.
International standards in 2030 were not the only area challenged by fragmentation. The longstanding intelligence relationships, such as the “Five Eyes,” on which the United States traditionally has relied, were not as productive as they were a decade ago. Digital threats to business, supply chain, and infrastructure continued to increase throughout the decade and, by 2030, the United States and its allies had found themselves on different sides in a number of regional conflicts. Although traditional force-on-force conflict had diminished over the decade, many countries followed the model pioneered by the Iranians, North Koreans, and Chinese in the early part of the decade and invested in offensive digital and cyber technology, training, and tactics. The lack of scientific breakthroughs and engineering progress in cybersecurity meant that many countries once considered to have “inferior” militaries found they could have an impact and be disruptive on a global stage. Where the United States had traditionally been able to focus much of its attention on a few major players, it became clear by 2030 that, owing to digital vulnerabilities and the ease of creating significant mischief, almost any country, or even cross-border criminal gangs and skilled individuals, had to be regarded as a serious threat to national security. The rise in various forms of cybercrime, including ransomware and fraud, continued to challenge the ability for national and international law enforcement to keep pace. A challenging economic landscape in many parts of the world meant that cyber cartels were able to take advantage of a technically sophisticated population and put them to work. In such an environment, with multiple and shifting adversaries, it became challenging for the United States to have a coherent policy to deter and respond to such mischief and threats.
With the continued lack of attention paid to cybersecurity over the decade, most efforts to break into systems were at least moderately successful and rarely detected before countries or criminals could achieve their aims. Companies and governments are under a constant barrage of attacks across the globe. Major IT companies drag their heels on compliance with a growing tangle of Federal regulations; as just one example, they still have not implemented the exceptional access mechanisms that permit authorized parties to unlock phones and other devices for law enforcement purposes. Most citizens agree with the companies’ positions as they fear an overly intrusive Federal government; university students not only actively demonstrate against such mechanisms and initiatives but many refuse to serve in the military or join the Intelligence Community. The torrent of data from the IoT has essentially obliterated privacy. (Of course, intelligence agencies around the world purchase as much personal data as they can afford. To some extent they do not need extensive collection capabilities as industry is doing it for them.) There have been proposals that consumers could “opt out” of such intrusive collection by paying a monthly service fee, but at present this seems unlikely.
Warning Signals for Scenario 5
Table 5.5 summarizes some key developments associated with Scenario 5, along with warning signals that might indicate to the Intelligence Community that this scenario is emerging.
Risks and Opportunities in Scenario 5
Although “The Known World, Only More So” might appear similar to “The World Today in 2030,” the combination of Predictable, Fragmented, and Chaotic presents a challenging and complex operating environment for the Intelligence Community. In this scenario, there is no quantum computing or classical cryptographic break driving a sense of urgency or advantage/disadvantage, and that gives a number of global competitors (countries and non-state actors) a chance to catch up. In addition, the combination of Fragmented and Chaotic will lead to a constantly contested information environment.
Risks for the Intelligence Community in Scenario 5 include the following:
- Challenge for defense: Buggy implementation of PQC combined with an uneven rollout will create weak software systems—perhaps weaker than if the post-quantum transition had not been attempted.
- Deteriorating or diminished partnerships: Fewer national alliances, and those that survive will be more transactional or issue focused.
TABLE 5.5 Key Developments and Warning Signals for Scenario 5: The Known World, Only More So
| Development | Warning Signal |
|---|---|
| “Without the sense of urgency that a cryptanalytic breakthrough would drive, global society has been slow to make the transition to post-quantum cryptographic algorithms for the past decade. Forward-leaning companies and countries have invested time and money into the effort, but the transition has been uneven across the globe, resulting in incompatibility, introducing bugs and, in some cases, creating new vulnerabilities or breaking existing communications infrastructure.” | With no cryptanalytic breakthrough (quantum or traditional) is the Intelligence Community seeing a messy and slow transition to post-quantum encryption? |
| “Further complicating the issue, the transition from 5G to 6G was messy and uneven across the globe. This combination of circumstances contributed to making life easier for ‘offense’ over the course of the decade, as there were plenty of bugs in systems to exploit, driven by a reliance on poor quality code, inconsistent support for patching of security vulnerabilities, and a lack of common standards.” | Is the transition from 5G to 6G messy and are threat actors taking advantage of the “messiness”? Is offense gaining or maintaining an advantage over defense? |
| “In response to these rumors, the EU launched its own ‘independent’ algorithm standardization process, which itself was beset with controversy after a set of leaked e-mails suggested that the Brainpool elliptic curve parameters had been manipulated by Germany’s BSI to permit a previously unknown trapdoor of unknown cryptanalytic impact.” | Is the European Union (or any other similar major government) appearing to prioritize its own standardization process and deemphasize international standards? |
| “Only vestiges of the open web, e-mail, and other network protocols that dominated the history of the public Internet remain. Instead, communications and information have been mediated largely through individual apps. Users have become accustomed to installing custom ‘region’ drivers and virtual private network (VPN) software that installed the national algorithms, local government root certificates, and other cryptographic parameters required to access network resources in a given country.” | Do the open web and Internet protocols look the same worldwide, or are communications mediated through apps? To what extent are countries locking down access to the Internet and requiring users to take additional country-unique steps to access it? |
| “The long-standing intelligence relationships, such as the ‘Five Eyes,’ on which the United States traditionally has relied, were not as productive as they were a decade ago. Digital threats to business, supply chain, and infrastructure continued to increase throughout the decade. and, by 2030, the United States and its allies had found themselves on different sides in a number of regional conflicts.” | How are allied relationships progressing? Are there issues that are straining traditional alliances? |
- Rise of national or regional technology requirements: The rise of regional information networks will require international software vendors to support multiple versions of software, including encryption technologies, to meet national or regional requirements. This will present an economic and business challenge, but also force the Intelligence Community to design specific collection strategies and resources for each region and drive the cost of technical and human resource investments.
- Narrowing lead for U.S. Intelligence Community: Because there have been no technology breakthroughs and, hence, no sense of urgency, other competitors have had time to catch up, narrowing the advantage of U.S. intelligence. This means that smaller and smaller state and sub-state entities will have the capability to launch attacks that, at the very least, will be disruptive and require Intelligence Community attention.
- Disinformation drives poor investments: This scenario has no breakthroughs, but how can the Intelligence Community be certain? Rising disinformation over the 2020s poses a risk that, although intelligence assessments might not show the existence of quantum computers, policymakers may make decisions or force investments as if a foreign adversary were on the cusp of developing one.
- Shifting scope and authorities: As cyberattacks and data breaches are constant and on the rise in this scenario, the Intelligence Community will be under pressure to focus on protecting U.S. and allied infrastructure more broadly.
Opportunities for the Intelligence Community in this scenario include the following:
- Offensive advantages: A Fragmented and Chaotic scenario presents challenges for defense, but it should also present a wealth of offensive opportunities for the Intelligence Community. There will be many divergent implementations, each with its own bugs to be exploited. The lack of interoperability owing to regionalization might also lead to more plaintext or weakly protected information being accessible. In addition to more opportunities, the attacks can be more aggressive because regionalization will limit second- and third-order impacts resulting from disclosure and repurposing of U.S. offensive tools and techniques against U.S. and allied entities.
- Take advantage of time: In a Predictable scenario, there is time to invest in transitioning critical systems to post-quantum encryption, spending “what it takes” to overcome chaotic system development and operation before the threat becomes a crisis.
Actions Relevant to Scenario 5
- Resource a smooth transition to post-quantum algorithms: These algorithms should be standardized and then adopted within the Intelligence Community as soon as possible. In some cases, this will require new hardware in addition to new software—for example, PQC certificates may exceed embedded hardware memory sizes. It would be a mistake to gradually “trickle out” post-quantum algorithms; upgrades should be identified, prioritized in the budget, and done quickly.
- Maintain trust: International buy-in to the NIST standardization process is important for a smooth post-quantum algorithm transition timeline. As discussed in Chapter 2, this trust has been challenged in the past by reactions to the actions of the U.S. government. The Intelligence Community should tread carefully in the future to avoid further loss of trust or derailing of goodwill, both of the U.S. public and the international community.
- Take steps to unify the global tech industry around a common core of algorithm and protocol standards: NIST is best positioned to lead this effort from within the U.S. government, but the Intelligence Community can play a very important role both in bringing cryptographic expertise to bear, and in strongly encouraging American industry to prioritize such actions. To the extent that government requirements are practical and align with the needs of the private sector, U.S. government purchasing can play a role here.
- Invest in better software, hardware, and infrastructure: The Intelligence Community should gain a clear understanding of what software and hardware it is relying upon, and then prioritize efforts to transition to better software, hardware, and infrastructure security, and advocate within the U.S. government for measures to improve security broadly in both the government and private sectors.
- Put serious effort into understanding IoT metadata and its utility: In this scenario, innumerable aspects of daily existence are affected by the IoT. These devices already spew a remarkable torrent of metadata (Internet traffic patterns, location information). It is the committee’s view that this trend is likely to continue, and with a vast increase in IoT devices, could prove a fountain of unexpected information. This will surely be a long-term effort as new forms of IoT are constantly being introduced to the market.
- Understand the vulnerabilities of 5G/6G, particularly its software-defined aspects, and how they might be exploited: 5G and the nascent 6G technologies bring a number of changes to mobile telephony infrastructure, most notably in how services are deployed across distributed clouds. This is new and highly complex technology for most telecommunications companies, and it is unclear how well it will be implemented and operated; on the face of it, there may be substantial chances for new vulnerabilities.
- Continue to grow “star” IT talent within the Intelligence Community: Of course, the Intelligence Community will always need expert technologists to build and operate systems, but in this scenario highly talented engineers and technicians will become more and more valuable to the Intelligence Community. Such talent is obviously in very high commercial demand, and as such commands reimbursement far beyond what the U.S. government can pay. Nonetheless, the Intelligence Community has some of these “stars” for whom
mission and patriotism outweigh financial gain. In this scenario, the Intelligence Community should do everything within its power to recruit, hire and retain these stars.
SCENARIO 6: COLONY COLLAPSE
Scenario 6, “Colony Collapse,” the final scenario the committee chose to explore for this report, explores a notional future described in Table 5.6. A variation on Scenario 6 is offered in Box 5.2.
In 2024, a European mathematician published a paper about a new more efficient way of factoring large numbers. Other researchers noticed the paper and began to explore its nuances, expand on its theoretical basis, and develop experimental software to assess its potential impact. Initial results were ambiguous, but some researchers continued to pursue the direction. Two years later, in 2026, a team of researchers from Europe, Japan, and the United States announced the ability to factor 1024-bit keys for the RSA encryption algorithm much faster than any previous result. More importantly, their technique would enable factoring of the 2048-bit keys in common use in only a million core-years, a level that would be feasible for governments or large companies or criminal groups.
Vendors and standards bodies responded with disbelief and confusion. Some vendors proposed removing support for 2048-bit keys from their products—in 10 years. Standards bodies argued about the best way to adapt to the new threat. The academic research community was confident that this advance would not affect the classical security of elliptic curve cryptography, but these algorithmic details typically got lost in translation in the media. Commercial products that incorporated post-quantum encryption algorithms which would not be affected by rapid factoring were still years in the future, and most current software could not accommodate RSA keys longer than 2048 bits, much less the key lengths of post-quantum algorithms. Some vendors suggested that users change 1024-bit keys weekly or move to discrete logarithm-based algorithms like Diffie-Hellman, even though the algorithmic advance was, after a bit of confusion, extended to this case as well within a few years. When asked, NSA referred reporters to its Commercial National Security Algorithm Suite defined in the Committee on National Security Systems Policy 15 (CNSSP-15), which permits use of RSA and Diffie-Hellman with 3072-bit or larger keys.
TABLE 5.6 Scenario 6: Colony Collapse
| Scenario Title | Driver Endpoints | Highlight |
|---|---|---|
| Colony Collapse |  |
A breakthrough in factoring and a lack of focus on systems and security puts information at risk. Despite advances in computing on encrypted data, trust remains low. |
| Scenario Description | ||
|
This scenario posits a breakthrough in the form of a new classical factoring algorithm. Such a breakthrough would render the public key encryption algorithms we rely on more easily attacked with much less effort than today, including by conventional computers. In this case, there would be much less need for a quantum computer. A roomful of powerful servers might be sufficient. Compared to a quantum computing breakthrough, a factoring breakthrough would probably have less advance notice, be easier to keep secret, and be attainable by more countries. In addition, a lack of focus on systems and security puts information at risk in this scenario. Despite advances in computing on encrypted data, trust remains low. This suggests, overall, a much more chaotic world combined with, as in the other scenarios, a more fragmented world politically. In this scenario, the Intelligence Community has to be on the lookout for a breakthrough that will be less easily discerned and more easily hidden than a large-scale quantum computer. Such a breakthrough could come via the efforts of a government or from academic cryptographic researchers. In either case, there might not be advance notice that such a breakthrough was about to occur or had occurred. Experts will debate the likelihood of such a factoring breakthrough, but it seems prudent to ask what would happen should it occur and what steps would need to be taken at that point. As in the other scenarios, much would depend on the ability of the U.S. government to mobilize the private sector to take the necessary steps as well. As with the other scenarios, international fragmentation—of technical standards as well as governmental relations—complicates the challenges for the Intelligence Community. Many governments react to internal tensions and fragmentation by weakening or imposing limits on the use of encryption, further facilitating attacks on encryption. In some respects, the results in this scenario are potentially more widespread and more dangerous than in the other two scenarios, giving added urgency to examinations of the likelihood and consequences of this breakthrough happening. |
||
While vendors and standards bodies disputed a path forward, hackers, cybercriminals, and nation-states were quick to exploit the new breakthrough. Malware was found circulating with a forged digital signature from a trusted 1024-bit key in an obscure part of Microsoft’s code-signing infrastructure related to extended long-term support of legacy operating systems. This was the beginning of a deluge of forged signatures. Forged software updates were a huge problem: a number of automobiles and wireless devices were rendered completely inoperable and had to be replaced. Worse yet, malicious updates to a wide range of devices began to cause havoc: home video cameras began streaming to the public at large, microwave ovens overheated, one type of gasoline pump kept pumping gas even after the tank was overflowing.
As vendors began a “rapid transition” to post-quantum encryption, they encountered further obstacles. NIST and agencies of several other governments had certified multiple post-quantum public key signature and encryption algorithms by 2023 but the certified algorithms were incompatible with each other, and the protocol specifications
and software that would be needed to use those algorithms were late (2032–2033) and buggy. In an abundance of caution, NIST had specified that implementations of its standardized post quantum algorithms be used in combination with classical public key algorithms, so that both would have to be defeated to accomplish a successful attack. This too caused issues, as the resulting complexity led to bugs in many implementations. Some industry-specific standards (e.g., wireless, automotive) simply ignored NIST’s guidance in favor of specialized algorithms whose security against attack had not been thoroughly vetted.
The multiplicity of standards and the residue of a global Internet and global commerce mean that most products and systems must implement several PQC suites (at least NIST, China, one other). The complexity of the resulting protocols and software leads to implementation errors that introduce further points of attack. A few “minimal” implementations for governments or security enthusiasts appear to be sound but achieve little or no adoption because of their (lack of) usability and functionality.
Warning Signals for Scenario 6
Table 5.7 summarizes some key developments associated with this scenario along with warning signals that might indicate to the Intelligence Community that this scenario is emerging.
Risks and Opportunities in Scenario 6
Scenario 6, “Colony Collapse,” is highly complex and dysfunctional. Great powers are jockeying for territory and influence across a series of constantly changing alliances, while all advanced nations suffer near daily breakdowns in some aspects of their appliances, services, and IT infrastructure. The combination of Disruptive, Fragmented, and Chaotic will prove highly challenging for the Intelligence Community: not only will it be extremely hard to predict or shape events, but even routine actions such as holding a virtual meeting may be disrupted without much warning. Employee morale may be very poor given such a difficult work environment.
The lack of mature hardware/software systems has a profound impact on this scenario. If software were better prepared and controlled, it might be a manageable task to determine which systems are susceptible to malfeasance and avoid them. In this scenario, however, everything from databases to doorbells has software of unknown and fluid provenance. This would seem likely to engender a high degree of distrust in all such systems, as one never knows what will fail next.
Risks and opportunities for the Intelligence Community have some similarities with the Scenario 1, “Quantum Breakthrough,” but differ in two key points:
TABLE 5.7 Key Developments and Warning Signals for Scenario 6: Colony Collapse
| Development | Warning Signal |
|---|---|
| “In 2024, a European mathematician published a paper about a new more efficient way of factoring large numbers. Other researchers noticed the paper and began to explore its nuances, expand on its theoretical basis, and develop experimental software to assess its potential impact. Initial results were ambiguous, but some researchers continued to pursue the direction. Two years later, in 2026, a team of researchers from Europe, Japan, and the United States announced the ability to factor 1024-bit keys for the RSA encryption algorithm much faster than any previous result.” | Has the Intelligence Community seen improvements in number field sieve or other algorithms that may open up new research directions related to factoring, discrete log, or other problems underpinning major public key standards? |
| “Software updates were a huge problem: a number of automobiles and wireless devices were rendered completely inoperable and had to be replaced. Worse yet, malicious updates to a wide range of devices began to cause havoc: home video cameras began streaming to the public at large, microwave ovens overheated, one type of gasoline pump kept pumping gas even after the tank was overflowing.” | Is there a marked increase in the prevalence of malware or bogus software updates with apparently valid digital signatures? |
- It is more difficult to see a classical analytic breakthrough coming than a full-scale quantum computer, so the timelines to react are much more compressed.
- Lack of mature hardware/software systems leads to a much higher degree of chaos.
The sections below first list those risks that are shared with the “Quantum Breakthrough” scenario, so the reader does not need to flip pages back and forth, then explicitly call out additional risks for this scenario. These risks are shared:
- Recruiting, hiring, and retaining the “best and the brightest”: Employee quality is a key risk. Will the United States and the Intelligence Community have the talent to be successful, particularly if the United States ceases to attract students and faculty from around the world?
- Weakening and shifting alliances: In a fragmented scenario, the United States should not assume that traditional long-term allies remain. As trust and collaboration recede, collection efforts grow more expensive and will surely need deep triage. With ever-shifting bilateral alliances, it may be hard (slow) to pivot to new targets or allies; and it is unwise to share important secrets with any other nation which seems likely to switch alliances.
- Too many targets: If each country, or each region, is using its own unique system or form of encryption, it is possible that the Intelligence Community would not have the resources to monitor and penetrate all systems of interest. Fragmentation of the scenario’s information infrastructures increases the cost of intelligence collection from information systems, as every system requires its own tailored implementation.
Risks for the Intelligence Community in this scenario that are not shared with the “Quantum Breakthrough” scenario include the following:
- Analytic breakthroughs could create very high risk at short notice: Encrypted communications or stored data whose protection relied on vulnerable public-key encryption that an adversary has collected or saved may—without much warning—suddenly be at risk of decryption and exploitation. Once such information is collected, there is nothing the originator can do to protect it, but there is a need for an inventory, assessment of potential damage, and development of mitigation plans. In addition, any stolen data that was secured at rest by such encryption would also be revealed.
- Reliance on untrustworthy hardware/software systems could create very high risk: As employees increasingly rely on everyday systems of uncertain quality, there is a real chance that cryptanalytic breakthroughs could magnify the risk of collapse of “everyday” appliances and services that their operators had presumed were protected from malicious access by strong encryption. In the worst cases, such breakthroughs could make it extremely difficult for employees to perform their jobs. Of course, this risk also carries over into official government systems that employ commercial hardware or software.
- Perennial need for high-quality mathematicians: In order to maintain technical expertise, the Intelligence Community requires a steady stream of students to receive a high-quality, Ph.D.-level education in mathematics or computer science. Those students should be U.S. citizens able to be approved for a security clearance. Historically, the U.S. government has hired mathematicians without background in cryptography and trained them itself. This approach has worked well in the past but appears to be falling behind. In particular, the transition to PQC requires expertise in different areas of mathematics from classical public-key cryptography. In 2015, researchers from Government Communications Headquarters (GCHQ), a key Five Eyes partner to NSA, took the unusual step of engaging with the open cryptographic research
community about the cryptanalysis of a candidate post-quantum lattice-based cryptographic scheme they had designed.5,6,7,8
Opportunities for the Intelligence Community in this scenario include the following:
- Easy pickings: A “Fragmented and Chaotic” scenario presents a wealth of attack/offensive opportunities for the Intelligence Community. There will be many divergent implementations, each with its own bugs to be exploited; and many suddenly vulnerable to cryptanalytic attack (decryption, use of malign signatures, etc.). The lack of interoperability owing to regionalization might also lead to more weakly encrypted information being accessible. In addition to more opportunities, the attacks can be more aggressive because regionalization will limit the potential for reuse of attack techniques on U.S. or allied systems.
- Misattribution of attacks: Fragmented society and governance plus chaotic systems might enable the U.S. government to hide an offensive cryptanalytic breakthrough if they discover it and disguise the resulting exploitation as software exploitation.
- Spurred investment in cryptographic defense: An actual cryptanalytic advance would certainly be a great opportunity to push for more investment in defense. It would be well after the fact, but there’s nothing like a crisis to spur development.
Actions Relevant to Scenario 6
The sections below first list those actions that are shared with the “A Brave and Expensive New World” scenario, so the reader does not need to flip pages back and forth, then explicitly call out additional risks for this scenario. These actions are shared:
- Move to mature systems: This will require enormous effort across the United States, as the current status is at the “chaotic” end of the spectrum for nearly all systems. It is not clear that anyone really understands the implications of good cybersecurity because there is no real-world experience to draw on. It is also unclear how to move toward such systems in practice although the 2021 cybersecurity executive order appears to be an attempt to move in that direction. This issue is much larger than the Intelligence Community and would require effort from major companies, researchers and start-ups, educational institutions, and the U.S. government. It is likely that very heavy investments would be required for research but especially for real-world implementations. As mature systems become available, the Intelligence Community must introduce new, more resilient IT very quickly (not over decades) and as needed abandon less-important IT infrastructure that cannot be quickly secured.
- Focus on ensuring that the United States can provide an adequate supply of high-quality, trustworthy staff: Although the large number of foreign-born students in STEM is a major blessing for our country, it should not be taken as a given and may not continue. The U.S. government should work toward considerable improvement in K–12 mathematics and science education, in particular. Advanced cryptographic research is poorly and unevenly funded in the United States; steady, long-term funding should be available for graduate students in cryptography and for efforts that may lead to mature systems (e.g., practical assured programming languages).
___________________
5 P. Campbell, M. Groves, and D. Shepherd, n.d., “Soliloquy: A Cautionary Tale,” https://docbox.etsi.org/Workshop/2014/201410_CRYPTO/S07_Systems_and_Attacks/S07_Groves.pdf.
6 Cryptanalytic Algorithms Group, “Soliloquy,” Google Groups Conversation, original post February 8, 2015, https://groups.google.com/g/cryptanalytic-algorithms/c/GdVfp5Kbdb8.
7 P. Campbell, M. Groves, and D. Shepherd, n.d., “Soliloquy: A Cautionary Tale,” https://docbox.etsi.org/Workshop/2014/201410_CRYPTO/S07_Systems_and_Attacks/S07_Groves_Annex.pdf.
8 R. Cramer, L. Ducas, C. Peikert, and O. Regev, 2016, “Recovering Short Generators of Principal Ideals in Cyclotomic Rings,” February 25, https://web.eecs.umich.edu/~cpeikert/pubs/logunit.pdf.
- Limit/mitigate fragmentation, both in technologies and between the United States and allies: The Intelligence Community and the United States will need to consult with current allies, and try to leverage purchasing power to push common standards and increase implementation maturity. The Intelligence Community will need to emphasize its efforts to preserve existing relationships with allies, but plan to potentially pivot toward new, perhaps short-term relationships. Such a pivot will require both political resources and tending such relationships. Last, because technology fragmentation is a key feature of this scenario, the Intelligence Community needs to learn new technologies and standards; there will be many more of them than at present, and with a higher rate of disruptive scientific advances.
An action for the Intelligence Community that is unique to this and not shared with the “Quantum Breakthrough” scenario:
- Continuously analyze the potential real-world impacts of a cryptanalytic breakthrough: This should be done on an ongoing basis because reliance on cryptographically secured systems continues to grow rapidly. Efforts to protect U.S. critical infrastructure would be a good starting point: for example, how would a sudden breakthrough affect the U.S. financial system, electric grid, food distribution, hospitals, and so on. This could be augmented with analysis of the impact to employees’ daily lives for crippling of such systems, or other “everyday” technology such as refrigerators, furnaces, automobiles. As the scope of such potential vulnerabilities becomes clearer, perhaps some “Plan B” or remediation approaches could be thought out.
SUMMARY OF RISKS AND OPPORTUNITIES
Although the exploration of these three scenarios allowed committee members to explore a variety of different possibilities, one clear objective of this effort was to identify those areas that would be common across the scenarios. Preparing for the risks and opportunities that appear in multiple scenarios will be one way that the Intelligence Community can increase the likelihood that it will be able to mitigate those risks or take advantage of those opportunities as they begin to emerge. Table 5.8 provides a summary of common areas across the scenarios.
SUMMARY OF ACTIONS
In each of the scenarios described above, the committee identified specific actions the Intelligence Community could take to prepare for the risk and opportunities that might present themselves. Table 5.9 highlights those actions that are relevant in two or three of those worlds. These actions would represent the “no regret bets” for the Intelligence Community, because they would provide a benefit, regardless of the operating environment.
TABLE 5.8 Commonalities Across the Scenarios
| Risk | Description |
|---|---|
Weakening or shifting alliances
|
In all three scenarios, the Intelligence Community is faced with the challenge of building alliances. While each of these scenarios includes the “Fragmented” Society and Governance driver, that is no accident, because the committee believes that it is the most relevant to explore. For this risk, it appears that the endpoints in the other two drivers are not irrelevant, but simply provide different details to a similar narrative: The Intelligence Community, and the United States, will need to invest resources into strengthening existing alliances and/or building new ones over the coming decades. With ever-shifting bilateral alliances it may be hard (slow) to pivot to new targets or allies; and it is unwise to share important secrets with any other nation. The Intelligence Community, and the United States, will need to consider how it shares information and perhaps look more to transactional, ad hoc, arrangements, rather than traditional alliances that dominated the previous decades. |
Recruiting, hiring, and retaining the “best and brightest employees”
|
In both Scenarios 2 and 6, finding and retaining qualified personnel becomes a challenge. Both are at the “Fragmented” and “Disruptive” endpoints of their respective driver, and this combination will present a challenge. A few reasons for this challenge emerged from discussions among committee members:
|
Multitude of targets
|
In both Scenarios 2 and 6, the combination of “Fragmented” and “Disruptive” seems to drive each country to seek its own unique system or form of encryption. If that is the case, then it is possible that the Intelligence Community would not have the resources to monitor and penetrate all systems of interest. With less data crossing borders, and higher “walls” protecting the information, the Intelligence Community will not be able to focus resources on choke points and will have to rely on more resources or identify “insiders” within the countries themselves to support data collection. |
TABLE 5.9 Summary of Preparations That Would Be Beneficial in Two or More Worlds
| Action | Description |
|---|---|
Move to mature systems
|
This will require enormous effort across the United States as the current status is at the “chaotic” end of the spectrum for nearly all systems. It is not clear that anyone really understands the implications of good cybersecurity because there is no real-world experience to draw on. It is also unclear how to move toward such systems in practice, although the 2021 cybersecurity executive order appears to be an attempt to make an initial move in that direction. This issue is much larger than the Intelligence Community and would require effort from major companies, researchers and start-ups, and the U.S. government. It is likely that very heavy investments would be required for research and especially for real-world implementations. |
Focus on ensuring that the United States can provide an adequate supply of high-quality, trustworthy staff
|
Although the large number of foreign-born students in STEM is a major advantage for the United States, it should not be taken as a given and may not continue. The U.S. government should work toward considerable improvement in K–12 mathematics and science education in particular. It should also encourage college and university computer science and software engineering departments to treat competence in building secure systems as a fundamental requirement for all students. Advanced cryptographic research is poorly and unevenly funded in the United States; steady, long-term funding should be available for graduate students in cryptography and for efforts that may lead to mature systems (e.g., practical assured programming languages). |
Limit/mitigate fragmentation, both in technologies and between the United States and allies
|
The Intelligence Community and the United States will need to consult with current allies, mobilize other government agencies including NIST, and try to leverage purchasing power to push common standards and increase implementation maturity. The Intelligence Community will need to emphasize its efforts to preserve existing relationships with allies, but plan to potentially pivot toward new, perhaps short-term relationships. Such a pivot will require both political resources and tending such relationships. Last, because technology fragmentation is a key feature of each scenario, the Intelligence Community needs to learn new technologies and standards; there will be many more of them than at present, and with a higher rate of disruptive scientific advances. |
Focus on alliances
|
While the alliances might look different in 2040 (and in each scenario), the Intelligence Community will still depend on partners to support its offensive and defensive operations. Whether those alliances are long-standing and deep-seated or ad hoc and built to meet specific needs will be determined by the operating environment. The Intelligence Community will need to take steps today, however, to prepare for a more fragmented world in 2040. |



















